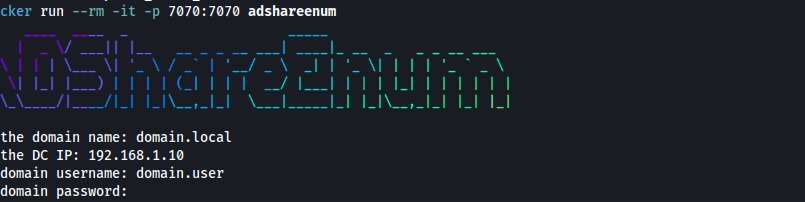
During internal assessments or red team engagements, identifying misconfigured shares in an Active Directory environment is a key step for privilege escalation and lateral movement. That’s why I built ADShareEnum, a Dockerized...
Category - tutorial
Recently, I was working on an Active Directory lab where the challenge was to extract a password stored in a user’s description field. I successfully completed the task using CrackMapExec on my primary computer. However...
1. Filter by IP address: “ip.addr == x.x.x.x”, where “x.x.x.x” is the IP address you want to filter 2. Filter by IP address range: “ip.addr >= x.x.x.x and ip.addr <= y.y.y.y”, where...
In this post I would like to talk about shadow credential attack that can be exploited by abusing AddKeyCredentialLink privilege in an Active Directory Infrastructure. 1-What is shadow credential ? It is a technique allowing an...
Recently, I’ve discovered a new way to escalate privilege on windows through WSUS when HTTP protocol is used instead of HTTPS. In this quick explanation I’ll describe what WSUS is, explain how to detect the vulnerability and...