Have you ever heard of CrackMapExec ?
CrackMapExec (a.k.a CME) is a post-exploitation tool that helps automate assessing the security of large Active Directory networks.
It took part in enumeration and exploitation of many protocols like smb, ssh, ldap, winrm, mssql.

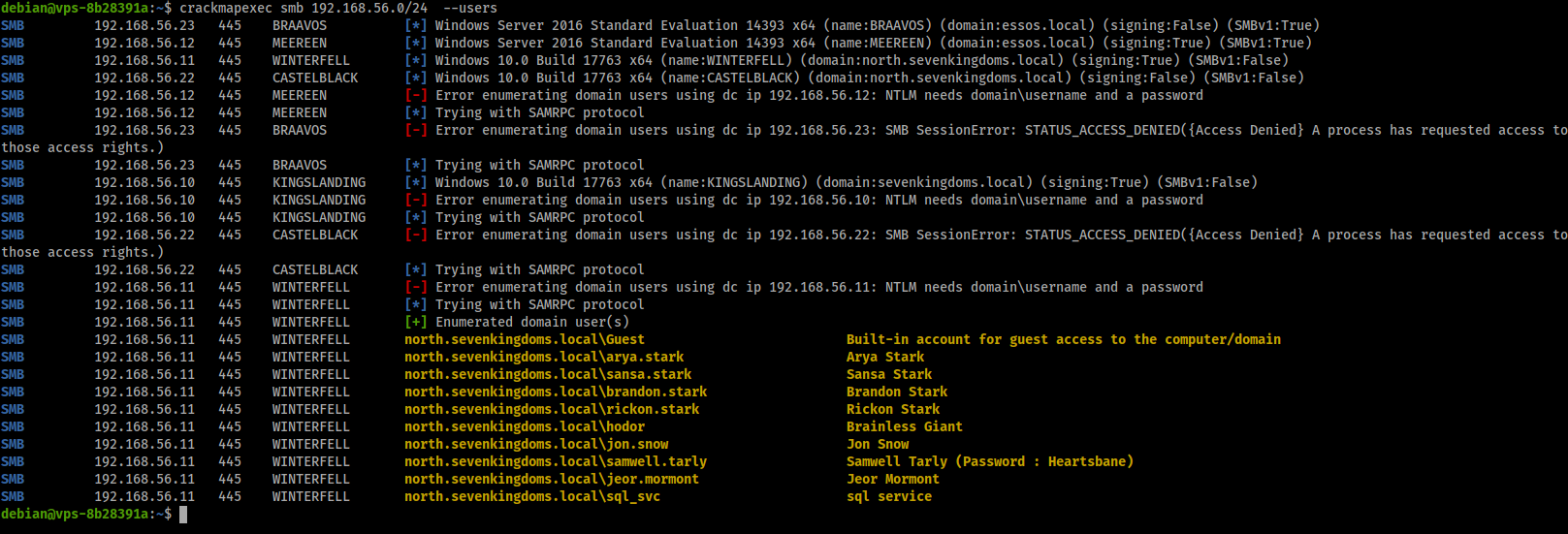
Each module has a list of available plugins useful for many purposes. In smb for example, you can enumerate users if anonymous session is allowed on a specif domain controller.
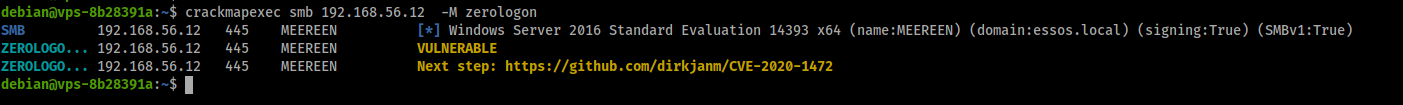
You can also use zerologon plugin to check if any domain controller machine is vulnerable to Zerologon (CVE-2020-1472). The following picture shows an example of how this can be used.
Then from now on, don’t forget to include crackmapexec in your tool list during a pentest engagement !